March 31, 2026, was one of those days when the industry looked less like a machine and more like a pile-up. Anthropic accidentally shipped a release of Claude Code that exposed a large internal codebase through a source map. X had a U.S. outage the same day. OpenAI reported elevated failures for some ChatGPT Enterprise and Edu users joining workspaces through SSO. Anthropic's own status history also shows timeouts affecting Claude Opus 4.6 and Sonnet 4.6 from March 31 into April 1. Then, as if the point still needed proving, reporting linked a major supply-chain attack on the widely used Axios npm package to North Korean operators.
None of these incidents share one root cause. Together, though, they point at the same operating reality: modern delivery stacks are fast, brittle, and still too trusting of packaging and release machinery.
The Anthropic incident is the one people will remember. A security researcher, Chaofan Shou (@Fried_rice), found that @anthropic-ai/claude-code version 2.1.88 had been published with a roughly 60 MB cli.js.map file. That artifact made it possible to reconstruct a very large portion of the underlying TypeScript code. Anthropic said no customer data or credentials were exposed and described the event as a release-packaging error caused by human error, not a security breach. That distinction matters. It also does not let anyone off the hook.
My take: the ugliest leaks are often not glamorous. No zero-day. No movie-grade exploit chain. Just a release pipeline that let the wrong artifact cross the last gate.
Intro
What makes this case interesting is not just the size of the leak. It is the shape of it. Anthropic did not lose model weights. It did not leak customer prompts. It leaked what many teams quietly treat as "just build output." That is the trap. Build output is not harmless. A source map can be as revealing as the source itself if it lands in the wrong place.
That is why this story belongs in a wider frame. The same week brought service instability, identity friction, and a supply-chain compromise through npm. One event hurts availability. Another hurts trust. Another turns the package manager into an attack surface. Different symptoms. Same operating environment.
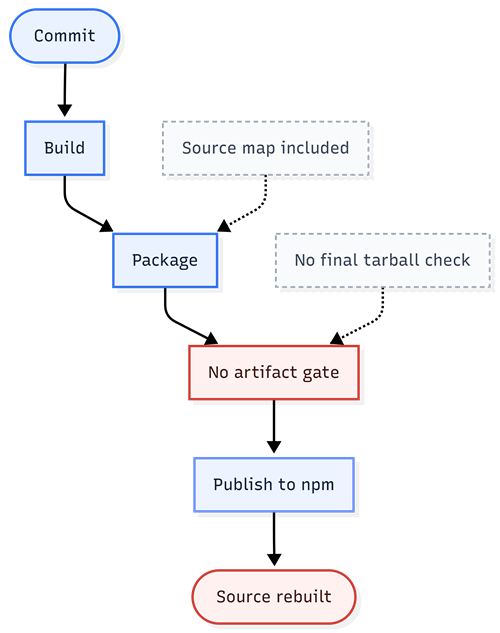
Figure 1. A plausible failure path in the Claude Code incident.
Root cause
At the narrowest level, the root cause was simple: a release artifact that should never have been published made it into a public package. Coverage and security write-ups agree on the mechanics. The version 2.1.88 of Claude Code included a source map file, and that file exposed internal code and feature details. Anthropic called it human error in packaging. That is probably true. It is also incomplete.
The deeper root cause sits in the release chain. Packaging is often treated as a boring last step, something the build system more or less handles on its own. That works right up to the moment it does not. Public registries do not know which files are harmless and which are dangerous. They will distribute whatever your pipeline hands them. If your process does not whitelist what is allowed to ship, scan the final tarball, and block debug artifacts at publish time, then a mistake like this is not a black swan. It is backlog debt waiting for a trigger.
This is also why the event feels bigger than one company's mistake. npm and similar registries are built for speed and convenience. That is good for distribution. It is bad for discipline if teams rely on convention instead of enforcement. The Axios compromise disclosed on March 31 shows the malicious version of the same structural problem: once a poisoned package or dependency enters a trusted path, downstream systems ingest it at machine speed. In Anthropic's case, the package was not malicious. In the Axios case, it was. The lesson is the same. The registry will ship whatever trust chain reaches it first.
Lessons learned
First, packaging is a security boundary. Many teams still behave as if security ends after code review, SAST, and secret scanning. It does not. The publishable artifact is the thing the world actually receives. That is what deserves the hard gate.
Second, source maps need a written policy. Either they are allowed for a reason and scoped to the right environment, or they are stripped from public distributions. "We usually do not ship them" is not a policy. It is a hope.
Third, release pipelines should scan the final package, not just the repository. A clean repository and a dangerous tarball can exist at the same time. Dry-run publishing, allowlists in package.json, and explicit checks for files such as *.map, .env, and build metadata are cheap controls compared with the cost of a public leak.
Figure 2. What the safer path should look like.
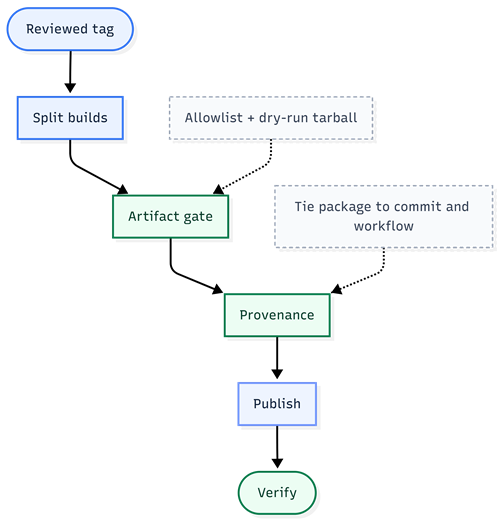
Fourth, provenance matters more now than it did a year ago. You do not need many supply-chain incidents before every public release becomes both a delivery event and a trust event.
Fifth, outage planning and release hygiene now belong in the same conversation. March 31 showed both sides of the problem. One set of incidents affected access and reliability. Another exposed code. A third abused the package ecosystem itself. If your product depends on AI providers, identity systems, and public package registries, your failure model is already composite. Your controls should be composite too.
The intentional leak theory
There is another angle worth addressing because it is already circulating in X threads and blog comments: what if this was not an accident at all? I get why people go there. Shipping a giant source map in a mature release flow sounds absurd on its face, and the leak immediately created buzz, community reverse-engineering, and a burst of attention around Claude Code. In a market where momentum matters, that makes the theory sticky.
But the public record does not get us there. Anthropic's public line is that this was a packaging error caused by human error, not a security breach. Boris Cherny, who leads Claude Code, also described it as human error during deployment. The coverage I could verify does not show Anthropic announcing that Claude Code is going open source. What I could find instead was outside interest in that idea, plus a wave of community forks and clean-room rewrites that took off after the leak.
Outside commentary also leans toward operational failure, not controlled disclosure. That does not rule out strategic benefit after the fact. It does make the deliberate-leak theory look unproven.
My read: it is fair to say the leak accidentally fed open-source momentum. It is not fair, based on current evidence, to say Anthropic planned it.
What's next?
Anthropic will almost certainly tighten its release process after this. That is the easy prediction. The harder question is whether the rest of the industry will read this as a one-off embarrassment or as a warning. It should be the second. The code leak was not a Hollywood breach. It was a packaging miss with very real consequences. Those are the incidents teams tend to underestimate until they happen to them.
For engineering leaders, the next step is not a vague call for "better security." It is specific. Make the artifact list explicit. Fail the build if debug files are present. Review the exact tarball that will be published. Separate debug builds from public builds. Add provenance where your tooling supports it. Rehearse package compromise response, not just infrastructure response. And if your organization ships internal CLIs, SDKs, or agent tooling through public registries, treat every publish as if it were a production deployment. It is.
The industry will move on from this story quickly. It always does. But the pattern will stay with us. Fast-moving teams, thin release gates, public registries, lots of automation, not enough suspicion. A series of unfortunate events? Yes. Also, a series of very preventable ones.
References
- Claude Code leak reporting and Anthropic statements: Axios, The Verge, BleepingComputer.
- Reuters reporting on the X outage on March 31, 2026.
- OpenAI and Anthropic status pages for the March 31 to April 1 service incidents.
- Reuters plus Google / Microsoft reporting on the Axios npm compromise and North Korea linkage.
- Outside commentary and supply-chain context: The Verge, Business Insider, and software supply-chain reporting.
Comments